What Is AES-256 Encryption? Why Your Document Platform Needs It
Published on April 22, 2026
What Is AES-256 Encryption? Why Your Document Platform Needs It
AES-256 encryption is the gold standard for securing digital data, using a 256-bit symmetric key that renders files practically uncrackable by modern computing power. For finance teams sharing sensitive documents such as investment memoranda, cap tables, and due diligence packages, any platform that cannot confirm AES-256 protection represents an unacceptable security risk. If your document sharing tool cannot show you its encryption specification, it is time to find one that can.
What AES-256 Actually Means
AES stands for Advanced Encryption Standard. The "256" refers to the key length: 256 bits. To brute-force a 256-bit key, an attacker would need to attempt 2^256 combinations, a number so large that even the most powerful supercomputers on earth would need longer than the age of the universe to crack it.
AES-256 is the same encryption standard used by government agencies, military organisations, and the world's largest financial institutions. When a document platform claims bank-grade security, AES-256 is usually the specific standard they are referencing.
There are two primary contexts where AES-256 applies to document sharing:
- At rest: The file is encrypted while it sits on the storage server, so even a server breach does not expose readable data.
- In transit: The file is encrypted as it moves between servers and the recipient's browser, typically via TLS combined with AES-256.
A secure document platform applies both.
Why Finance Teams Cannot Afford Weaker Encryption
Finance professionals regularly handle documents that carry material non-public information (MNPI): term sheets before signing, financial models before announcement, and investor reports before publication. A single breach can trigger regulatory investigations, reputational damage, and legal liability.
Under the EU's GDPR, organisations have an obligation to apply appropriate technical measures to protect personal data. If a finance document contains personal data, which many do when they include individual shareholder details or employee compensation schedules, AES-256 encryption is part of fulfilling that obligation.
Weaker encryption standards, such as AES-128 or RC4, are still considered acceptable in some contexts, but they offer a narrower safety margin. For sensitive financial documents, there is no reason to accept anything less than AES-256.
How SendNow Implements AES-256 Encryption
SendNow applies AES-256 encryption at every layer of its document infrastructure. Files are stored encrypted on AWS S3, the same infrastructure used by the world's most security-conscious enterprises. Every link generated by SendNow delivers document content over HTTPS with TLS encryption, so no readable data travels unprotected across the network.
This is not an optional add-on or a premium feature. Every document on every plan is encrypted by default, from the moment it is uploaded to the moment it is permanently deleted.
Comparing Document Platform Encryption Standards
| Platform Type | Encryption at Rest | Encryption in Transit | Key Length |
|---|---|---|---|
| Email attachment | None (server dependent) | TLS (varies) | N/A |
| Generic cloud storage | AES-256 (most) | TLS | 256-bit |
| Consumer file sharing | AES-128 to AES-256 | TLS | 128–256-bit |
| SendNow | AES-256 | TLS + HTTPS | 256-bit |
The critical difference between generic cloud storage and a purpose-built platform like SendNow is not just encryption: it is the combination of encryption with access control, audit logging, and revocation. Encryption alone does not stop an authorised recipient from forwarding a link or downloading and redistributing a file.
Encryption Is Necessary but Not Sufficient
A common misconception is that encrypted storage equals secure document sharing. Encryption protects data from external attackers who breach the storage layer, but it does not protect against insider threats, accidental over-sharing, or link forwarding. Once an authorised user has access to a document, encryption has already done its job and cannot prevent further distribution.
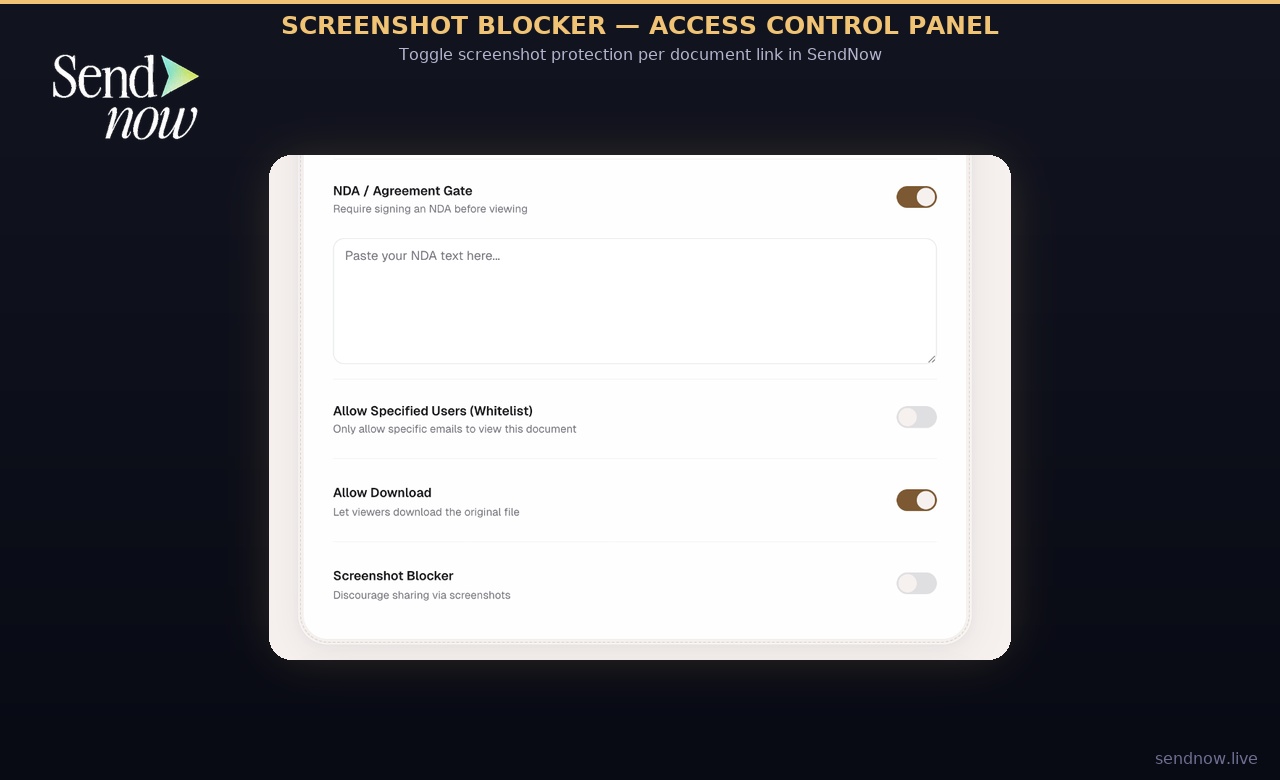
This is why leading finance teams pair AES-256 encryption with:
- Access expiry: Links that stop working after a set date or number of views
- Watermarking: Viewer-specific marks that deter and trace leaks
- Revocation: The ability to kill a link instantly, at any time
- Audit logs: A full record of who accessed the document, when, and from where
Together, these controls create a security posture that encryption alone cannot achieve.
What to Ask Your Document Platform
Before trusting a platform with sensitive financial documents, ask these questions:
- What encryption standard do you use for files at rest?
- Is encryption applied at upload, or only after processing?
- What key management practice do you follow? Are keys rotated?
- Is your encryption independently audited or certified?
- Does your platform comply with EU GDPR technical requirements?
A reputable platform will answer all five clearly. If any answer is vague, that is a signal to look elsewhere.
Related Reading
- The Complete Guide to Secure Document Sharing for Finance Teams
- What Is a Document Audit Trail and Why Do Finance Teams Need One?
- How to Permanently Delete a Shared Document From All Servers
Frequently Asked Questions
Q: What does AES-256 encryption mean for a shared document? A: It means the file is stored and transmitted using a 256-bit symmetric key, making it computationally infeasible for an attacker to decrypt the data without the correct key.
Q: Is AES-256 the same as bank-grade encryption? A: Yes. AES-256 is the encryption standard used by major banks, government agencies, and military organisations, which is why it is commonly described as bank-grade.
Q: Does AES-256 encryption prevent document leaks? A: Encryption prevents unauthorised access at the storage and transit level. It does not prevent an authorised user from sharing or leaking a document, which is why access controls, watermarking, and audit logs are also necessary.
Q: Is AES-256 required for GDPR compliance? A: GDPR requires appropriate technical measures to protect personal data. AES-256 is widely recognised as meeting that standard, particularly for high-sensitivity data categories common in finance.
Q: Can a document be decrypted by the hosting platform? A: Platform-managed encryption means the platform holds the keys and can technically decrypt files. For most business use cases, this is acceptable. For highly sensitive government or legal files, client-side encryption may be preferred.
Q: Does SendNow use AES-256 on all plans? A: Yes. AES-256 encryption is applied to every document on every SendNow plan by default.
Q: What is the difference between AES-128 and AES-256? A: Both are secure, but AES-256 uses a longer key, which provides a larger margin against future advances in computing power. For sensitive financial data, AES-256 is the preferred choice.
Q: How do I verify a platform uses AES-256? A: Ask the vendor directly, check their security documentation or trust page, and look for compliance certifications such as SOC 2 or ISO 27001, which require rigorous encryption standards.
Ready to share documents with bank-grade AES-256 encryption? Start your free trial at sendnow.live and protect every file you send.
Ready to share documents smarter?
Start tracking who reads your documents, page by page. Free trial, no credit card required.
Get Started for Free →