How to Share a CIM Securely With Potential Buyers
Published on April 22, 2026
How to Share a CIM Securely With Potential Buyers
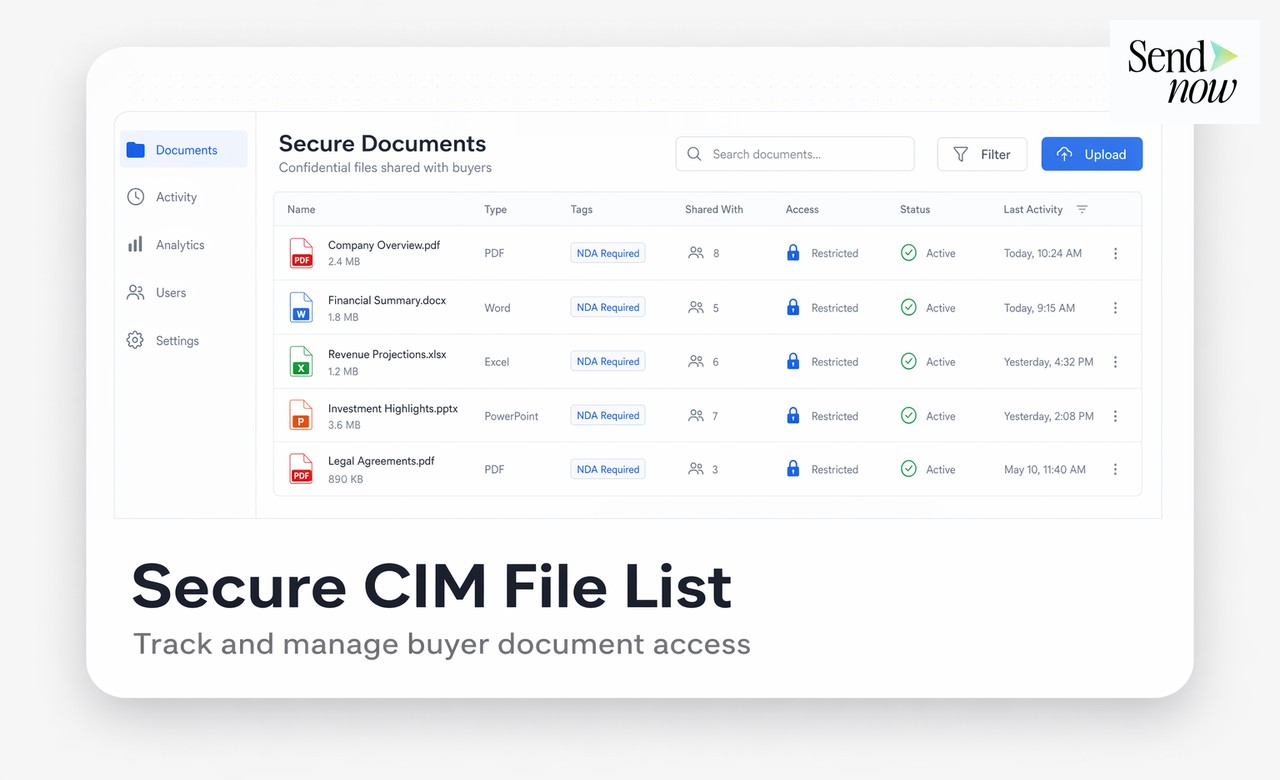
Sharing a confidential information memorandum (CIM) securely means ensuring that only verified, NDA-signed buyers can access your document, that every page is traced to the recipient, and that you retain full control over what they can do with it. Done correctly, secure CIM distribution protects deal confidentiality, prevents leaks, and gives you forensic accountability if something goes wrong.
What Is a CIM and Why Does Security Matter?
A confidential information memorandum is the primary marketing document in any M&A sale process. It contains revenue figures, customer data, operational details, and strategic plans — precisely the information that a competitor, a bad-faith buyer, or a leaky intermediary could exploit. In European deal markets, CIMs also frequently contain personal data covered by the GDPR, which adds a legal dimension to distribution security.
Traditional methods — attaching a PDF to an email, sharing via Dropbox, or using a generic WeTransfer link — offer no access control, no audit trail, and no way to revoke a document once it has been sent. A buyer can forward the file to twenty people, print it, or upload it to a competitor's server, and the seller has no visibility or recourse.
Gate Access Behind an NDA
The first control layer is making sure that no one reads the CIM without first signing a non-disclosure agreement. A proper NDA gate requires the recipient to accept terms before the document becomes visible — not just before they download it, but before they can see a single page.
With SendNow, you create a secure link that presents the NDA inline. The buyer signs digitally, their acceptance is timestamped and logged, and only then does the document viewer open. If they decline, the link shows nothing. This keeps your legal protections tight and gives you a signed record for every person who accessed the CIM.
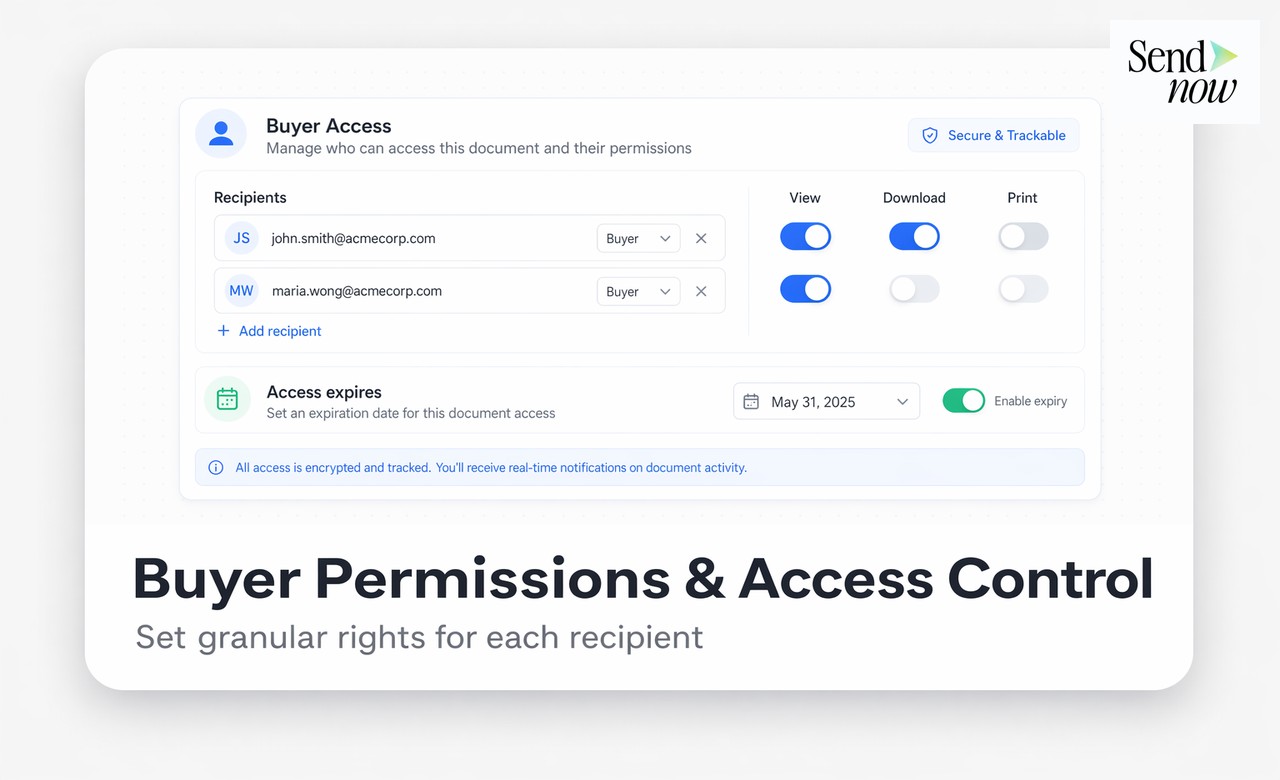
Disable Download and Printing
Requiring an NDA signature is not enough on its own. If a buyer can download a clean PDF copy, the NDA becomes difficult to enforce — you cannot prove which copy was forwarded or printed. The better approach is to serve the CIM inside a secure viewer with downloading and printing disabled.
SendNow's access control settings let you block download, block printing, and block screen capture at the link level. The buyer reads the document in their browser. They cannot save a local copy. Combined with the NDA gate, this means there is only one controlled copy in circulation per buyer, and you know exactly who has it.
Apply Dynamic Watermarks
Even with download restrictions in place, a determined recipient could photograph their screen. Dynamic watermarking addresses this by embedding the buyer's name, email address, and access timestamp directly into every page of the document as it renders. The watermark is invisible to someone skimming the document normally, but clearly legible in any screenshot or photograph.
If a watermarked page appears in the press or lands in a competitor's inbox, you can identify the source immediately. That accountability alone is often enough to discourage casual leaks.
Control Expiry and Revocation
Deal processes move quickly and documents become stale. A CIM shared in week one may contain assumptions that are superseded by week four. Link expiry and revocation give you the ability to pull the document from circulation at any point — before a buyer completes their review, if a deal falls apart, or if a party withdraws from the process.
Set an expiry date when you create the link so that access lapses automatically. If circumstances change mid-process, revoke the link instantly from your dashboard. The buyer's next attempt to open the document returns an access-denied message. You do not need to contact them or rely on them deleting a local file.
Monitor Engagement Per Buyer
Secure distribution is not only about protecting information — it is also a deal intelligence tool. Knowing which buyer opened the CIM, how many pages they read, which sections they spent the most time on, and whether they shared the link with a colleague tells you a great deal about their seriousness and focus areas.
SendNow's visitor analytics give you page-level heatmaps and session timelines for every recipient. You can see if a buyer who claimed to be "reviewing the financials" never opened the financial section, or if an unexpected IP address accessed a link. This data helps you prioritise follow-up and spot irregularities early.
Secure CIM Sharing vs. Standard File Transfer
| Feature | Email Attachment | Dropbox/WeTransfer | SendNow Secure Link |
|---|---|---|---|
| NDA gate before access | No | No | Yes |
| Download disabled | No | No | Yes |
| Dynamic watermarking | No | No | Yes |
| Link expiry and revocation | No | Partial | Yes |
| Page-level analytics | No | No | Yes |
| GDPR-compliant audit log | No | No | Yes |
| AES-256 encryption at rest | Varies | Yes | Yes |
GDPR Considerations for CIM Distribution
If your CIM contains personal data — employee names, customer references, or individual financial data — GDPR Article 5 requires that it be processed with appropriate technical measures. Sharing an uncontrolled PDF with a list of third-party buyers does not meet that standard. A secure sharing platform with access logs, encryption, and the ability to delete data on request provides the documented safeguards that regulators expect.
SendNow is built for EU-based deal teams. All data is stored in European data centres and the platform provides a GDPR-compliant audit trail for every document access event.
Related Reading
- Virtual Data Room: The Complete Guide
- Private Equity Due Diligence Documents
- M&A Due Diligence Document Checklist
Start Sharing Your CIM Securely
SendNow gives M&A advisers and corporate finance teams a purpose-built platform to share CIMs with full access control, NDA gating, watermarking, and GDPR-compliant audit logs. Start your free trial at sendnow.live and distribute your next CIM with confidence.
Frequently Asked Questions
1. What is the safest way to share a CIM with a potential buyer? The safest method is to use a secure document link with an NDA gate, download restrictions, and dynamic watermarking. This ensures the buyer signs before accessing the document, cannot save an uncontrolled copy, and that every page is traced to their identity.
2. Can I share a CIM by email attachment? You can, but it is not recommended. An email attachment offers no access control, no audit trail, and no ability to revoke access. Once sent, you have no visibility into who else sees the document.
3. Does sharing a CIM require GDPR compliance in the EU? Yes. If the CIM contains personal data (employee names, customer data, individual figures), GDPR requires appropriate technical and organisational measures. This includes encryption, access logging, and the ability to delete data on request.
4. What is a dynamic watermark? A dynamic watermark embeds the recipient's name, email, and access timestamp into every page of the document as it renders. It is unique to each viewer, making it possible to identify the source of any leak.
5. How do I prevent a buyer from printing or downloading my CIM? Use a secure document viewer that disables download, print, and screen capture at the link level. The buyer reads the document in their browser without the ability to save a local copy.
6. What happens if I need to revoke CIM access after sending it? With a secure link platform, you can deactivate the link instantly from your dashboard. The buyer's next attempt to open the document will be denied, regardless of whether they bookmarked the URL.
7. How long should a CIM link remain active? Most deal teams set an expiry of two to four weeks, aligned with the indicative offer deadline. Some set a shorter window and extend on request, which also signals buyer engagement.
8. Can I see if a buyer has actually read the CIM? Yes, with a platform that provides per-recipient analytics. You can see open time, pages viewed, time spent per section, and whether a second device or IP address accessed the link.
Ready to share documents smarter?
Start tracking who reads your documents, page by page. Free trial, no credit card required.
Get Started for Free →