Audit Logs for Document Sharing: What They Track and Why It Matters
Published on April 24, 2026
Audit Logs for Document Sharing: What They Track and Why It Matters
#TLDR: Knowing that someone opened a document is useful. Knowing exactly which pages they read, for how long, whether they attempted a download, and whether they signed an NDA first is the difference between analytics and a proper audit trail. This guide covers what a complete document audit log must capture, why it matters for financial compliance, and how to export it for legal and regulatory use.
Table of Contents
- What Document Audit Logs Track
- Why They Matter for Financial Compliance
- The Difference Between Analytics and a True Audit Log
- What a Complete Audit Trail Must Include
- Using Audit Logs in Disputes, Regulatory Reviews, and Privilege Claims
- How to Export and Store Them Compliantly
- Comparison: Audit Log Depth by Platform Type
- FAQs
What Document Audit Logs Track {#what-audit-logs-track}
A document audit log records every meaningful interaction a viewer has with a shared file. At minimum this includes: when the link was opened, which pages were viewed, how long was spent on each page, whether a download was attempted, and when the session ended.
A complete audit log goes further. It captures the viewer's identity (name, email, company where collected), their IP address and geographic location, the device and browser they used, whether an NDA was presented and signed before access was granted, whether a return visit occurred, and whether a revocation event has since been triggered.
The purpose of an audit log is not to monitor individual behavior for its own sake. It is to create a durable, timestamped record that can answer two questions with certainty: who had access to this information, and what did they do with it during their session?
Why They Matter for Financial Compliance {#why-compliance}
Financial firms operating in the EU operate under several overlapping frameworks that either require or strongly benefit from document audit trails: GDPR (Article 5 accountability principle), MiFID II (record-keeping obligations for investment-related communications), DORA (digital operational resilience), and sector-specific guidance from the FCA, BaFin, and AMF.
None of these frameworks explicitly require a document-level audit log in every case. But each of them rewards firms that can demonstrate a systematic approach to access control and record-keeping. When a regulator asks whether a specific counterparty received material non-public information ahead of a transaction, the answer cannot be "we are fairly certain they did not." The answer needs to be a timestamped record.
Secure document sharing platforms that maintain complete audit logs give compliance officers something they rarely have: the ability to reconstruct the information flow around any sensitive document, after the fact, without relying on recipient cooperation.
The Difference Between Analytics and a True Audit Log {#analytics-vs-audit}
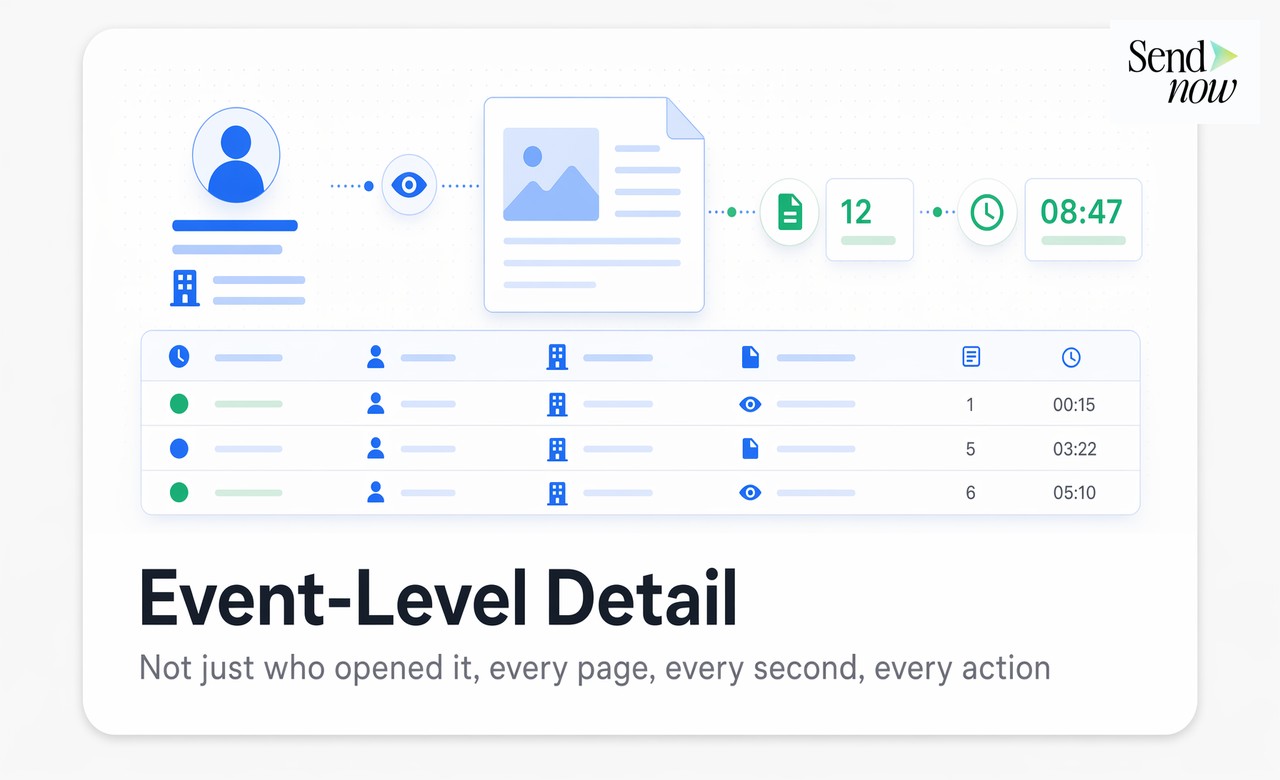
Most document platforms offer some form of engagement analytics. They tell you that a document was opened, often with a page count or a rough session duration. This is useful for sales teams assessing prospect interest. It is not useful for compliance.
The difference is specificity, immutability, and identity verification. Analytics aggregates behavior. An audit log records individual events with precision timestamps. Analytics may show that "a user" spent two minutes on pages 5 through 8. An audit log shows that "sarah.k@kkr-example.com, IP 185.12.xx.xx, signed NDA at 14:31 GMT, opened document at 14:32 GMT, viewed pages 1-14 in sequence, spent 6 minutes 42 seconds total, session ended at 14:39 GMT, no download attempted."
That level of specificity is what transforms a log from a dashboard metric into a legal instrument.
What a Complete Audit Trail Must Include {#complete-audit-trail}
For a document audit log to be useful in a legal or regulatory context, it needs to satisfy five criteria:
Identity linkage. The log must connect events to a verifiable identity, typically the email address of the viewer, cross-referenced against the NDA signature record where applicable.
Event granularity. Individual events must be timestamped separately: link opened, NDA presented, NDA signed, page X viewed, session ended, download attempted, document revoked. A single "accessed" timestamp does not constitute an audit trail.
Immutability. The log must be write-once and tamper-evident. A log that can be edited after the fact by the document owner has no evidential value.
Full agreement text. Where an NDA gate is in place, the audit record must preserve the exact text of the agreement that was signed, not a version reference or a hash.
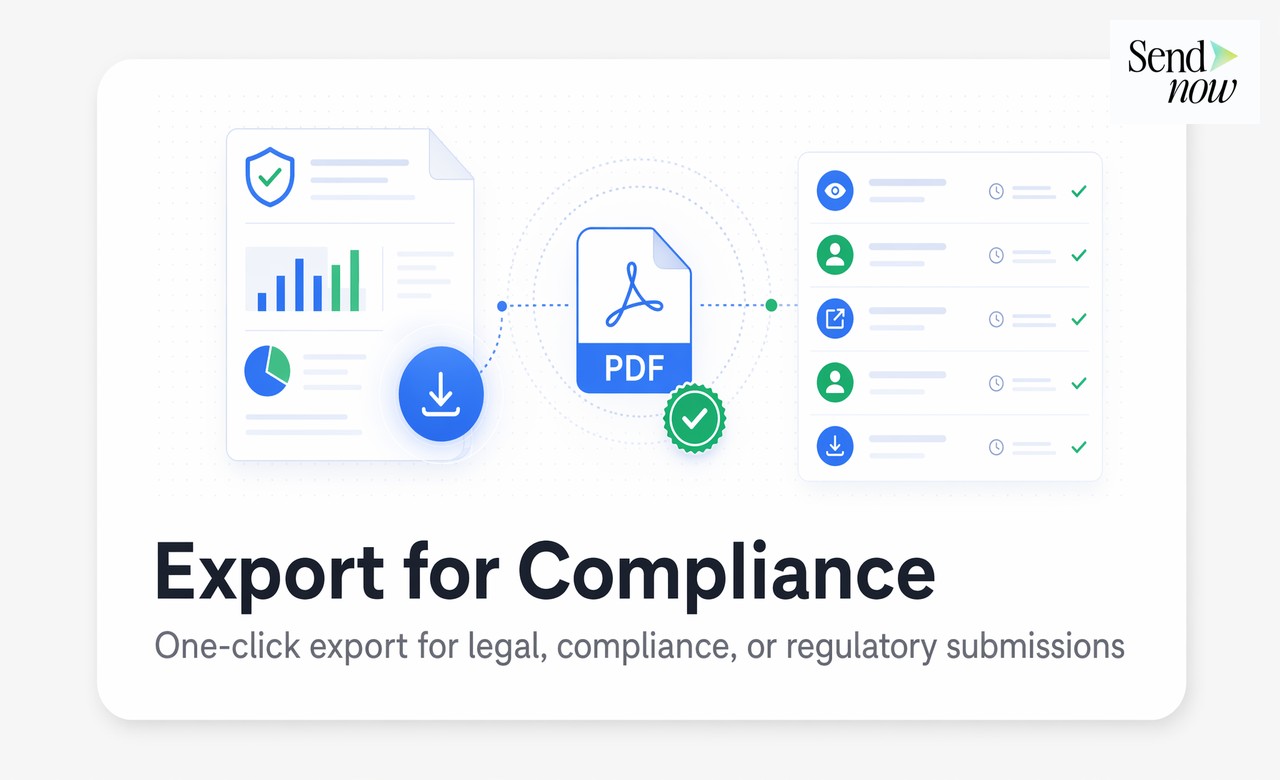
Exportability. The log must be exportable in a format usable by legal teams: at minimum a timestamped PDF, ideally also a structured data format for integration with compliance management systems.
Using Audit Logs in Disputes, Regulatory Reviews, and Privilege Claims {#using-audit-logs}
Audit logs serve three distinct legal functions in practice.
In commercial disputes, a log showing that a counterparty accessed your confidential financial model before making an offer introduces a factual record that challenges arguments about independent development or prior knowledge.
In regulatory reviews, a log demonstrating controlled access to material information supports arguments that a firm maintained appropriate information barriers. Regulators reviewing potential market abuse scenarios or insider trading allegations will ask for evidence of who had access to what and when. A complete audit log is direct evidence.
In privilege claims, audit logs help firms demonstrate that a document was handled with the level of confidentiality appropriate for privileged material. Courts in several EU jurisdictions have considered access control records when determining whether privilege has been waived through inadequate safeguarding.
How to Export and Store Them Compliantly {#export-store}
Under GDPR, audit logs that contain personal data (names, email addresses, IP addresses) are subject to data minimization and storage limitation principles. This creates a practical tension: you want to keep the log long enough to serve its compliance function, but not longer than necessary.
Best practice is to define a retention policy by document type. M&A transaction records may warrant a seven-year retention period aligned with corporate record-keeping obligations. General commercial proposals may need only two years.
SendNow supports one-click export of audit logs as PDF reports formatted for legal review, with all events, identities, and timestamps laid out chronologically. For firms with document management systems, the API allows automated export and archival. The export itself should be logged as part of the chain of custody for the audit record.
Comparison: Audit Log Depth by Platform Type {#comparison}
| Feature | Standard File Share (Dropbox, Drive) | Email + Read Receipt | Basic Doc Tracking Tool | SendNow |
|---|---|---|---|---|
| Page-level tracking | No | No | Sometimes | Yes |
| Viewer identity | No | Partial | Partial | Yes |
| NDA gate + signature record | No | No | No | Yes |
| Immutable log | No | No | Varies | Yes |
| Export for legal/compliance | No | No | Limited | Yes |
| GDPR-compliant storage | No | No | Varies | Yes |
FAQs {#faqs}
1. How long are audit logs stored on SendNow? Logs are retained according to your account's retention settings. Custom retention periods are available for enterprise accounts to align with your regulatory requirements.
2. Can a viewer see that they are being tracked? SendNow's privacy disclosure settings let you inform viewers that access activity is logged, which is a GDPR best practice where personal data is collected.
3. Are audit logs tamper-proof? Yes. Logs are write-once at the event level. Neither the document owner nor the platform can retroactively alter or delete individual log entries.
4. Can I export an audit log for a specific viewer only? Yes. You can filter the audit log by viewer email and export a report showing only that viewer's access history.
5. Does the audit log capture failed access attempts? Yes. Events such as failed NDA sign-off, revoked link access attempts, and expired link visits are all logged as distinct event types.
6. Is the audit log available via API? Yes. The SendNow API allows programmatic access to audit log data for integration with SIEM systems, compliance platforms, or custom reporting tools.
7. What happens to the audit log if I delete the document? Audit log records are retained independently of the document. Deleting a document does not delete its access history.
8. Is an audit log sufficient for MiFID II record-keeping purposes? An audit log is one component of a compliant record-keeping system. Consult your compliance officer to confirm that your full document workflow meets MiFID II obligations in your jurisdiction.
<script type="application/ld+json"> }, { "@type": "Question", "name": "Can a viewer see that they are being tracked?", "acceptedAnswer": { "@type": "Answer", "text": "SendNow's privacy disclosure settings let you inform viewers that access activity is logged, which is a GDPR best practice where personal data is collected." } }, { "@type": "Question", "name": "Are audit logs tamper-proof?", "acceptedAnswer": { "@type": "Answer", "text": "Yes. Logs are write-once at the event level. Neither the document owner nor the platform can retroactively alter or delete individual log entries." } }, { "@type": "Question", "name": "Can I export an audit log for a specific viewer only?", "acceptedAnswer": { "@type": "Answer", "text": "Yes. You can filter the audit log by viewer email and export a report showing only that viewer's access history." } }, { "@type": "Question", "name": "Does the audit log capture failed access attempts?", "acceptedAnswer": { "@type": "Answer", "text": "Yes. Events such as failed NDA sign-off, revoked link access attempts, and expired link visits are all logged as distinct event types." } }, { "@type": "Question", "name": "Is the audit log available via API?", "acceptedAnswer": { "@type": "Answer", "text": "Yes. The SendNow API allows programmatic access to audit log data for integration with SIEM systems, compliance platforms, or custom reporting tools." } }, { "@type": "Question", "name": "What happens to the audit log if I delete the document?", "acceptedAnswer": { "@type": "Answer", "text": "Audit log records are retained independently of the document. Deleting a document does not delete its access history." } }, { "@type": "Question", "name": "Is an audit log sufficient for MiFID II record-keeping purposes?", "acceptedAnswer": { "@type": "Answer", "text": "An audit log is one component of a compliant record-keeping system. Consult your compliance officer to confirm that your full document workflow meets MiFID II obligations in your jurisdiction." } } ] } </script>
Need a complete document audit trail for your firm? Try sendnow.live and get event-level logs, NDA records, and one-click compliance exports from day one.
Written by Alex Carter. Alex covers document security, compliance, and secure sharing workflows for financial and legal professionals across the EU.
Ready to share documents smarter?
Start tracking who reads your documents, page by page. Free trial, no credit card required.
Get Started for Free →