What Is an Audit Trail? A GDPR Guide for Finance Teams
Published on April 22, 2026
What Is an Audit Trail? A GDPR Guide for Finance Teams
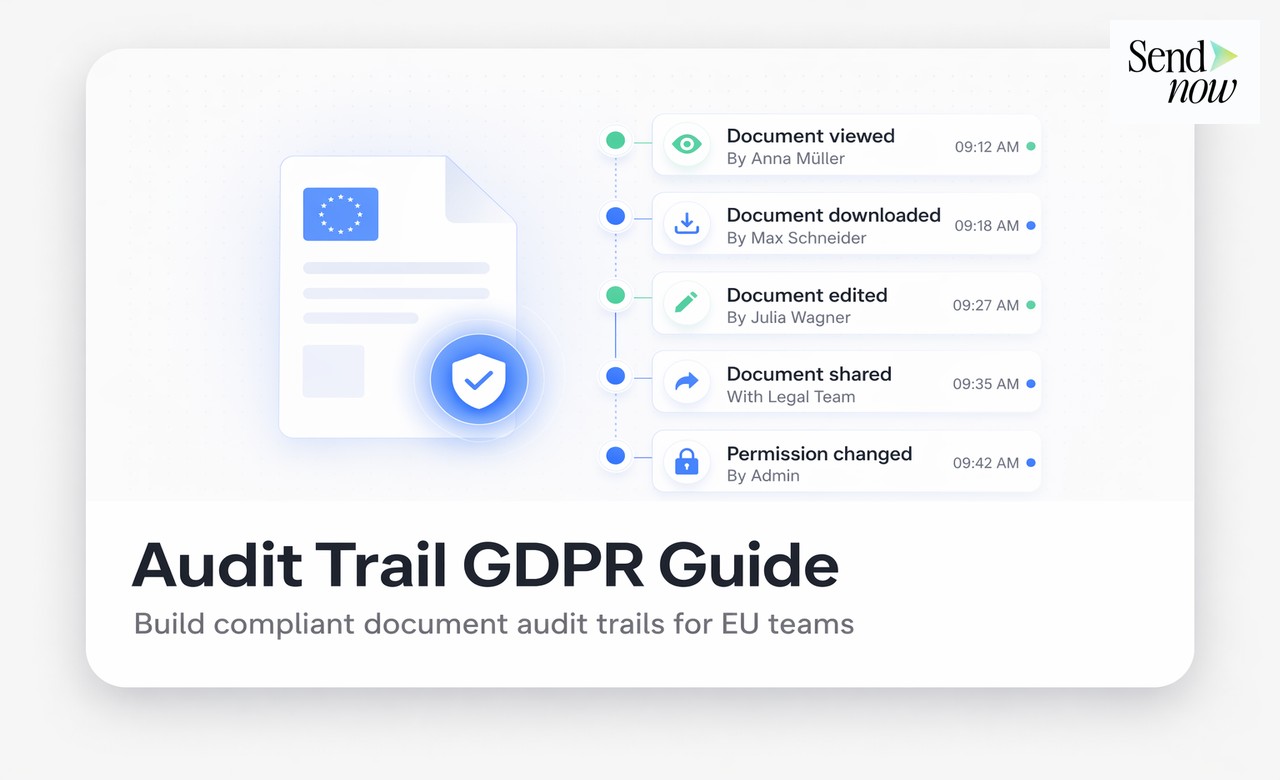
An audit trail is a chronological, tamper-proof record of all actions taken on a document or system, showing who did what, when and from where. Under GDPR, maintaining an audit trail for document sharing is not optional for finance teams — it is a practical requirement of the accountability principle in Article 5(2), which obligates organisations to demonstrate compliance with the Regulation. Without an audit trail, you cannot prove that sensitive financial documents were shared lawfully and securely.
Why Audit Trails Matter for Finance Teams Specifically
Finance teams handle some of the most sensitive personal data in any organisation: payroll records, shareholder information, client financial statements, tax documents and investor materials. Each of these document types carries GDPR obligations, and each creates potential liability if shared without appropriate controls.
An audit trail matters for finance teams because:
- Regulatory inquiries: Financial regulators in the EU increasingly ask for evidence that sensitive data was handled appropriately. An audit trail is the primary form of evidence.
- Data subject access requests: Under GDPR Article 15, individuals can request access to their personal data. An audit trail helps you identify exactly where their data was shared and with whom.
- Breach response: If a data breach occurs, an audit trail allows you to identify which documents were accessed, by whom and during what period — essential for GDPR's 72-hour notification requirement.
- Internal governance: Audit trails support internal controls by making document access visible to compliance officers and data protection officers.
What GDPR Requires You to Log
GDPR does not prescribe a specific format for audit trails, but the accountability principle in Article 5(2) and the security requirements of Article 32 together establish what must be recorded for document sharing:
Who shared the document: The identity of the person or system that created and distributed the document link or copy.
Who received access: The identity of each recipient, typically their authenticated email address or user ID.
When access occurred: The exact timestamp of each access event, including the first open and any subsequent return visits.
What was accessed: The specific document or document version, including any metadata that helps identify the content.
What actions were taken: Whether the recipient attempted to download, print, forward or otherwise act on the document.
From where access occurred: The IP address and device type, where technically feasible and proportionate.
When access was revoked: The date and time at which access was terminated, and by whom.
The Difference Between an Audit Trail and an Access Log
The terms are sometimes used interchangeably, but there is a practical distinction:
- An access log records raw system events — server requests, login attempts, file reads — typically at the infrastructure level.
- An audit trail is a curated, human-readable record of meaningful business events — specifically, who accessed a particular document and what they did with it.
For GDPR purposes, the audit trail is what matters. It provides context and meaning that a raw server log does not.
How Finance Teams Can Automate GDPR Audit Trails
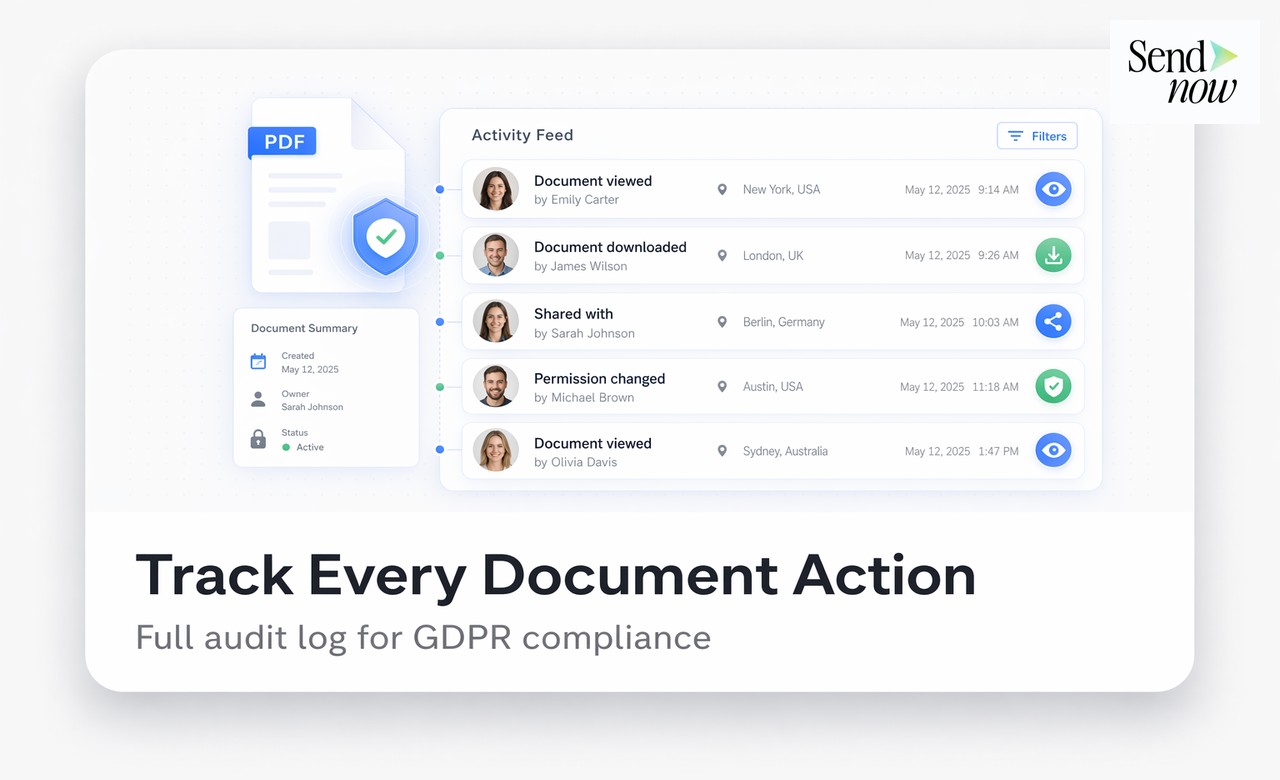
Manual audit trail maintenance — logging every document access in a spreadsheet — is impractical and error-prone. The solution is to use a document-sharing platform that generates the audit trail automatically.
Platforms such as SendNow record every access event automatically and present the data in a structured, exportable format. Finance teams can:
- Share a financial report, investor update or client statement via a secure link
- See, in real time, when each recipient opened the document
- Export the full access log as evidence of GDPR-compliant handling
- Set automatic expiry dates so documents are no longer accessible once the legitimate purpose has passed
This approach eliminates the burden of manual logging and produces a court-ready audit trail with no additional effort.
GDPR Article 5 and the Accountability Principle
Article 5(2) of GDPR states that the controller "shall be responsible for, and be able to demonstrate compliance with," the principles in Article 5(1). This is known as the accountability principle, and it has a direct practical implication: you cannot simply comply with GDPR — you must be able to prove it.
For document sharing in a finance context, proving compliance means demonstrating:
- That you had a lawful basis for each sharing decision
- That recipients were authorised to receive the data
- That appropriate technical measures were in place (encryption, access controls)
- That access was limited to the period necessary for the stated purpose
- That you can account for every access event
An automated audit trail from your document-sharing platform addresses all five of these requirements simultaneously.
How Long Should You Retain Audit Trail Records?
Retention periods for audit trails should reflect the documents they relate to:
- Financial contracts and statements: Align with your accounting retention policy, typically six to seven years under EU member state tax law
- Employee records: The period during which employment-related claims can be brought — typically up to six years after employment ends in most EU jurisdictions
- Investor documents: For the duration of the investment relationship, plus any statutory limitation period for claims
- Regulatory correspondence: As directed by the relevant regulator, typically a minimum of five to seven years
Document your retention policy and apply it consistently. Retaining audit trails longer than necessary is itself a GDPR data minimisation issue.
Related reading: GDPR and Document Sharing: Complete Guide | Best GDPR-Compliant File Sharing Tools for European Businesses (2026)
Audit Trail Requirements by Document Type
| Document Type | Minimum Audit Events | Retention Guidance |
|---|---|---|
| Investor financial model | Created, shared, accessed, revoked | Duration of fundraise + 6 years |
| Client financial statement | Shared, accessed by each recipient | 6–7 years from statement date |
| Employee payroll document | Shared, accessed, revoked | Employment period + 6 years |
| Board or investor report | Distributed, opened, returned to | 6 years from date of report |
| Cap table | Shared under NDA, accessed, revoked | Duration of investment + 6 years |
Frequently Asked Questions
Is an audit trail legally required under GDPR? GDPR does not explicitly mandate an audit trail in its text, but the accountability principle in Article 5(2) effectively requires one for any organisation that processes sensitive personal data. Supervisory authorities consistently expect to see documented evidence of data processing activities, and an audit trail is the primary mechanism for providing it.
What is the difference between an audit trail and a records of processing activities (RoPA)? A RoPA, required under GDPR Article 30, documents the categories of processing your organisation carries out. An audit trail records individual processing events. Both are required: the RoPA describes what you do; the audit trail proves you are doing it as described.
Can an audit trail be stored in a spreadsheet? A spreadsheet can serve as an audit record but it is not tamper-proof and is difficult to maintain accurately at scale. Purpose-built platforms that generate audit trails automatically are more reliable and more credible to regulators.
Who in a finance team is responsible for maintaining audit trails? The data controller is legally responsible — typically the organisation itself. In practice, the Data Protection Officer (DPO), the finance director or a designated compliance officer is accountable for ensuring audit trail processes are in place and functioning.
What should I do if I cannot produce an audit trail for a past document sharing event? If you are unable to produce an audit trail for a past event and a regulator requests it, document the gap, explain the reason (e.g., legacy process), and demonstrate what controls are now in place. Regulators consider remediation efforts when assessing enforcement action.
Does SendNow provide GDPR-compliant audit trails? Yes. SendNow automatically logs every access event for every document link — timestamped, attributed to the authenticated recipient and exportable in a structured format. All data is stored on EU-based infrastructure with AES-256 encryption.
How do I handle audit trail data subject access requests? If an individual submits a DSAR, they may request details of how their personal data was processed, including document sharing events. Your audit trail allows you to identify the relevant records and respond within the 30-day GDPR deadline.
Is an audit trail enough to prove GDPR compliance during an investigation? An audit trail is strong evidence but is most effective when combined with a documented lawful basis, a data protection policy, a DPA with your platform provider and staff training records. The audit trail demonstrates what happened; the other documents demonstrate that you had a lawful framework for it.
Ready to share documents smarter?
Start tracking who reads your documents, page by page. Free trial, no credit card required.
Get Started for Free →