Secure Document Sharing for Finance Teams: Best Practices
Published on April 2, 2026
Secure Document Sharing for Finance Teams: Best Practices
A practical guide to encryption, NDA gating, watermarking, and compliance for investment bankers, VCs, PE firms, and financial advisors.
Meta description: Learn the best practices for secure document sharing in finance. This guide covers AES-256 encryption, NDA gating, dynamic watermarks, screenshot protection, and GDPR compliance for financial teams in 2026.
TLDR
Finance teams handle some of the most sensitive documents in existence — term sheets, financial models, CIMs, LP communications, M&A materials. When shared insecurely, these documents create legal, regulatory, and reputational risk. This guide covers seven foundational best practices for secure document sharing, drawn from current GDPR requirements, financial services security standards, and the capabilities of leading platforms in 2026.
Introduction
In early 2025, a partner at a mid-market PE firm sent a confidential information memorandum to three potential buyers via email attachment. Within 36 hours, a screenshot of the company's EBITDA breakdown had circulated to a competitor. The file itself was password protected. The screenshot was not.
This is the defining security challenge for finance teams in 2026: the threat does not stop at the file level. It extends to every rendering of that file on every screen it reaches. Encryption protects data in transit and at rest. It does not protect against a recipient who presses Print Screen.
Secure document sharing for finance teams requires a layered approach. Encryption is the foundation. NDA gates control who gets in. Dynamic watermarks make leaks traceable. Screenshot protection closes the last mile. Access controls and expiry windows ensure documents do not outlive their authorization. A full audit trail satisfies the compliance requirements that govern every financial data room, investor communication, and M&A process.
This guide answers the seven questions finance teams most often ask about secure document sharing, and offers practical recommendations at each layer.
What Is Secure Document Sharing?
Secure document sharing is the practice of transferring documents to authorized recipients while maintaining control over access, distribution, and the persistence of that content after delivery.
Basic file sharing — email attachment, cloud storage link, general file transfer — moves content to the recipient's device. Once downloaded, the sender loses all control. The recipient can print, screenshot, copy, forward, or store the file indefinitely.
Secure document sharing works differently. Rather than transferring the file, the sender shares access to a controlled viewing environment. The document renders inside a web-based viewer that the platform controls. The platform enforces rules about what the viewer is allowed to do: download or not, print or not, screenshot or not. It requires the viewer to accept an NDA before they see a single page. It can expire access on a specific date. It can revoke access instantly.
Kiteworks identifies the core requirements for professional services firms as "encryption in transit and at rest, access controls, audit logging, and compliance with regulations like GDPR and HIPAA." For finance specifically, the requirements extend further to include NDA enforcement, watermarking, and screenshot deterrence.
The distinction matters because the regulatory and legal consequences of an insecure share in finance are not hypothetical. They are well-documented, costly, and often career-defining.
Why Do Finance Teams Need Secure Document Sharing?
Finance teams operate with information asymmetry as a core business dynamic. Investment bankers, VCs, PE firms, and financial advisors routinely possess material information about companies, deals, and transactions before that information becomes public. The improper disclosure of this information carries serious consequences: regulatory investigation, deal collapse, loss of client trust, and reputational damage that affects future deal flow.
The documents themselves are uniquely high-stakes. A confidential information memorandum contains everything a buyer needs to make an acquisition decision. A financial model contains the assumptions underlying a company's valuation. An LP update contains performance data that limited partners expect held in strict confidence. A term sheet contains negotiating positions that, if disclosed, could shift deal dynamics entirely.
MapleTech notes that "breaches often start small: a misplaced file, an outdated access list, or an unencrypted email." For finance teams, small mistakes carry disproportionate consequences.
The second driver is regulatory. GDPR, applicable to any organization handling personal data of EU residents, imposes strict requirements on how data is processed, stored, and shared. SEC regulations govern how certain communications with investors are maintained and disclosed. Financial services firms in most jurisdictions operate under data protection obligations that email attachments simply do not satisfy.
Glasscubes identifies the financial and reputational risks of non-compliance with GDPR as among the strongest drivers of investment in secure document sharing infrastructure — a point that resonates with any finance professional who has watched a competitor face regulatory scrutiny over a data handling incident.
What Encryption Standard Should Financial Documents Use?
AES-256 is the encryption standard that financial documents require. It is the same standard used by governments, military organizations, and financial institutions worldwide, and it is the standard strongly indicated by GDPR's Article 32 for protecting sensitive personal data.
AES-256 (Advanced Encryption Standard with a 256-bit key) provides symmetric encryption at a strength level that makes brute-force attacks computationally infeasible with current and foreseeable technology. Phoenix Strategy Group notes that financial institutions face "thousands of cyberattacks daily, with data breaches costing an average of $4.45 million in 2023" — a figure that makes robust encryption a straightforward return on investment.
For document sharing, AES-256 encryption protects documents both in transit (as they travel between servers and browsers) and at rest (as they sit in cloud storage). The AWS infrastructure that underpins platforms like SendNow provides AES-256 encryption by default, with AWS's GDPR compliance whitepaper confirming that AWS supports the technical and organizational measures required under GDPR Article 32.
GDPR Advisor notes that "where data is sensitive or the risk is high, encryption is often treated as mandatory" under regulatory enforcement decisions, even though GDPR formally takes a risk-based approach to specific technical measures.
What encryption does not cover is the rendered content on screen. A perfectly encrypted PDF can still be screenshotted, photographed, or printed. Encryption works as a foundation layer — it secures the file in storage and transit — but additional controls are required to secure the viewing experience itself.
How Does NDA Gating Protect Confidential Financial Documents?
NDA gating is the practice of requiring a recipient to electronically accept a non-disclosure agreement before they can view a document. It is the digital equivalent of the physical NDA signing that preceded entry to a traditional data room.
The mechanism works within the secure document viewer: when a recipient clicks a tracking link, they see the NDA before any document content loads. They must accept the terms — which creates a timestamped record of their consent — before the document becomes visible. This provides two layers of protection.
First, it creates a legal record. If confidential information is subsequently disclosed in violation of the NDA, the sender has a timestamped acceptance log with the viewer's name, email address, and IP address. This substantially strengthens any legal action for breach of confidence.
Second, it acts as a deterrent. Recipients who know their identity is logged against their NDA acceptance are considerably less likely to share or misuse confidential content than recipients who receive an anonymous attachment.
Carta's data room documentation describes the NDA gate as requiring the viewer to acknowledge that "the Receiving Party hereby agrees to hold the Proprietary Information in strict confidence and to take all reasonable precautions to protect such Proprietary Information." For M&A processes, fundraising rounds, and any situation involving material non-public information, NDA gating is a minimum security requirement.
SendNow includes NDA gating as a standard feature on all plans, which is notable given that many competing platforms restrict this to enterprise tiers. Combined with email verification — which confirms the recipient's identity before they reach the NDA — it closes the most common gap in document security: the unidentified viewer who gains access through a forwarded link.
What Are Dynamic Watermarks and How Do They Deter Document Leaks?
A dynamic watermark is a watermark that changes based on the identity of the viewer. Unlike a static watermark that prints "CONFIDENTIAL" identically on every page for every viewer, a dynamic watermark embeds information specific to the recipient: their email address, IP address, access timestamp, or a combination of identifiers.
The security impact is significant. When a document with a dynamic watermark is photographed or screenshotted and shared externally, the image contains a forensic trail pointing directly to the person who leaked it. This is not a theoretical deterrent. Finance professionals are well aware that confidentiality breaches carry professional and legal consequences. The presence of a visible, personalized watermark on every page changes the risk calculation for anyone considering an unauthorized share.
Locklizard describes dynamic watermarking as delivering "watermarks that are far more effective and useful" than static alternatives, with the ability to embed information that changes per user, per session, or per page. CM-Alliance adds that "files travel fast. A report you send to a teammate can be shared beyond your control. Watermarking helps you mark files in a hidden way... making unauthorized sharing traceable."
For financial documents — CIMs, board packs, investor updates, model outputs — dynamic watermarks are the most practical deterrent against casual leaking. They do not stop a determined bad actor with physical printing equipment, but they eliminate the low-effort screenshot-and-forward behavior that accounts for the majority of confidential information leaks in practice.
Digify notes that dynamic watermarks work "across multiple formats, including PDFs, Office files, images, video, and audio" and support up to four identifiers such as text, email, IP address, and date or time.
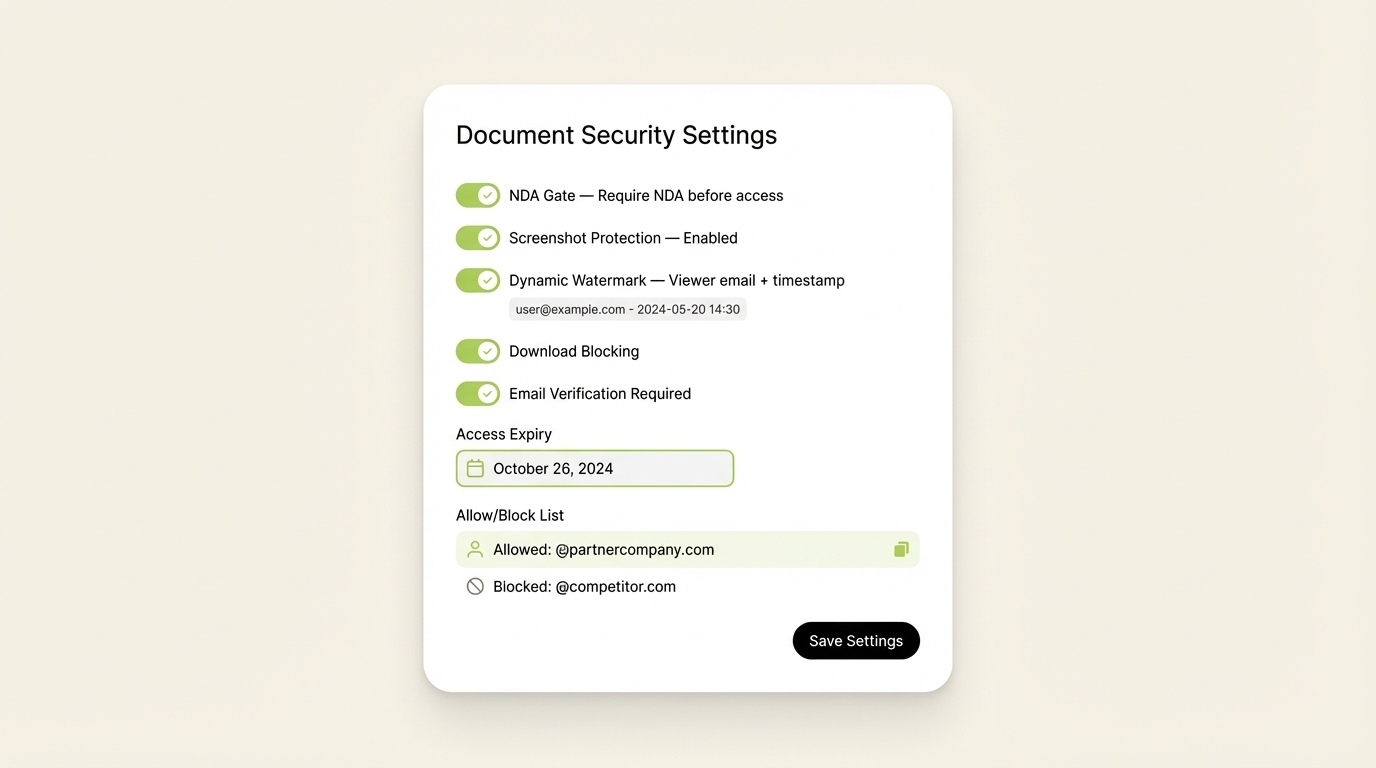
A fully configured document security setup: NDA gate, screenshot protection, dynamic watermark, download blocking, and expiry — all in one control panel.
How Does Screenshot Protection Work for Shared Documents?
Screenshot protection is a feature that attempts to block or detect screen capture attempts on documents viewed inside a secure web viewer. It operates at the browser level: the platform's viewer uses browser APIs and behavioral signals to detect and, where possible, prevent screenshot capture.
The technical limits are real. A browser-based screenshot block cannot intercept a physical camera pointed at a screen. But it stops the majority of casual and opportunistic capture attempts: keyboard shortcuts, screen recording software, Print Screen key, and OS-level screenshot tools triggered within the browser environment.
VeryPDF documents how financial institutions have adopted DRM solutions specifically to prevent unauthorized screenshots of quarterly financial statements, noting the risk that "someone might take screenshots, stitch them together, and leak our sensitive data."
Peony.ink's 2026 guide on PDF screenshot protection identifies the documents most at risk as "investor financials, M&A due diligence documents, enterprise pricing, a board pack" — precisely the materials that finance teams share most frequently.
FileCloud's DRM documentation describes how the "Secure Web Viewer provides DRM protection by ensuring that the physical document can be viewed but is never actually shared with recipients" — a viewer that "prevents screenshots, screensharing, and printing" within the controlled browser environment.
In practice, screenshot protection works best in combination with dynamic watermarking. Even if a screenshot does get captured through a physical camera or an OS-level tool the browser cannot intercept, the dynamic watermark ensures the image contains viewer-specific identification data. The protection layers reinforce each other: one layer deters, the other traces.
SendNow's real-time analytics and security controls in action — built specifically for finance professionals managing sensitive deal documents.
What Compliance Regulations Govern Financial Document Sharing?
Finance teams operating across jurisdictions face multiple overlapping compliance frameworks. The most significant are:
GDPR (General Data Protection Regulation): Applies to any organization handling personal data of EU residents. Article 32 requires "appropriate technical and organizational measures" to protect personal data, and encryption is explicitly cited as a recommended safeguard. GDPR Advisor notes that "where data is sensitive or the risk is high, encryption is often treated as mandatory" under regulatory enforcement decisions.
SEC and FINRA regulations: US financial services firms face recordkeeping and communication archiving requirements under SEC Rule 17a-4 and FINRA Rule 4511. Document sharing platforms need to support audit trail generation and archivable logs to satisfy these requirements.
SOC 2: While not a regulation, SOC 2 Type II certification is increasingly expected by institutional clients and LPs as evidence of a vendor's security posture. Platforms maintaining SOC 2 certification have undergone independent audits of their security controls.
PCI DSS: Relevant for any document sharing involving payment card data. Financial services firms that share documents containing card data must ensure those documents are handled within PCI DSS-compliant infrastructure.
AWS compliance framework: Platforms built on AWS infrastructure benefit from AWS's own compliance certifications — including ISO 27001, SOC 1/2/3, and GDPR alignment. As documented in the AWS GDPR whitepaper, AWS supports the technical measures required under Article 32, which extends to all applications hosted on its infrastructure.
For finance teams, the practical implication is clear: email attachments, consumer cloud storage, and general-purpose sharing links do not satisfy these requirements. A purpose-built platform with AES-256 encryption, access logging, expiry controls, and GDPR-compliant infrastructure addresses the compliance foundation. Soaring Towers frames it well for financial professionals: "without proper safeguards, you risk exposing confidential information, which can lead to data breaches and lost trust" — repercussions that are "both financial and reputational."
Conclusion
Secure document sharing for finance teams is not a single tool or a single setting. It is a layered security architecture: AES-256 encryption at the foundation, NDA gating to control entry, email verification to confirm identity, dynamic watermarks to trace any leak, screenshot protection to block opportunistic capture, download blocking to keep documents within the controlled environment, and a full audit trail for compliance.
The finance professionals who get this right share a common characteristic: they treat document security as a deal risk, not an IT issue. A leaked CIM can kill an M&A process. A screenshotted LP update can damage a fund's reputation irreparably. A term sheet forwarded to the wrong party can collapse a negotiation.
SendNow was built specifically for this risk environment — combining every layer of the security stack with branded deal rooms and real-time page-by-page analytics, at pricing that starts at $12/month. If your team still shares financial documents via email attachment or generic cloud links, start a free trial at sendnow.live. No credit card required.
Keep Reading
- How to Send Financial Documents Securely to Clients
- Email Attachments vs Secure Links: Why Finance Teams Are Switching
- GDPR Compliance for Document Sharing: What Finance Teams Must Know
- How to Block Screenshots on Confidential Business Documents
- What Is Dynamic Watermarking and Why Finance Teams Need It
Ready to share documents smarter?
Start tracking who reads your documents, page by page. Free trial, no credit card required.
Get Started for Free →